1 “Does anybody really know what time it is? Does anybody really care?” — Chicago, 1969 Perhaps...
In Depth
Yes — dd — the disk destroyer. The command that strikes fear into the hearts of SysAdmins...
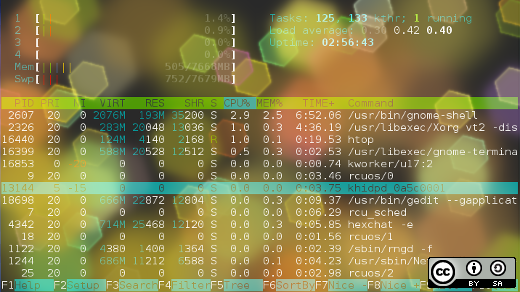
In a previous article, 4 open source tools for Linux system monitoring, I looked at tools like...
The base64 command converts binary data to ASCII data so that it can be transmitted as text....
Author’s note: This article is excerpted in part from chapter 5 of my book, The Linux Philosophy...
In previous articles about my use of automation in performing post-install tasks for new Linux installations, Those...
SSH is an important mechanism for secure connections between Linux hosts. SSH is a software-based virtual private...
Image via Creative Commons, modified by Both.org Introduction There are many different ways of protecting a system,...
In a recent article, I introduced the chown command, which is used for modifying ownership of files...
Image by: Opensource.com CC-by-SA 4.0 Every file and directory on a Linux system is owned by someone,...
2 Every object on your Linux system has a permission mode that describes what actions a user...
How my easy, home-made backup program saves time, space on the storage medium, and network bandwidth


How my easy, home-made backup program saves time, space on the storage medium, and network bandwidth
Nothing can ever go wrong with my computer and I will never lose my data. Riiiiight.
This article...
Adding a user is one of the most fundamental exercises on any computer system; this article focuses...
Understanding the boot and Linux startup processes is important to being able to both configure Linux and...
Take a walk through EXT4's history, features, and optimal use, and learn how it differs from previous...
A comparison of Linux commands for escalating privileges for non-root users